Disclaimer: All views presented here, in this newsletter, are my own.
Author or the newsletter are not liable for any actions taken by any individual or any organization / business / entity. The information provided is for education and awareness purposes only and is not specific to any business and or situation.
Hello friends,
Hope you are doing well. This marks the 60th edition of Securing Thing newsletter.
For those that are new and curious… and those that wants a quick recap.
Here’s a living index of all series (current/future) - make sure to ✍️ bookmark this.
Will be a featured post on newsletter main page and I’ll keep updating it.
Here’s a list of topics no particular order:
🧑🎓 Getting started in IT & OT Cybersecurity Series - 12 step career Transformation Blueprint (on-going: 4 steps published).
✍️The OT Security Dozen - a 12 Part series on Building an OT/ICS Cybersecurity Transformation Program (on-going: 4 parts published).
📘 ISA/IEC 62443 Standards Overview Series (on-going: 5 parts published).
↪️ IT/OT Cybersecurity Program Transformation Series - Multiple strategies.
↪️ Cybersecurity & AI across IT-OT Automation Stack - Monthly Digest.
↪️ The Digital Factory Cybersecurity - Digital Transformation & AI Risks.
📲Misc. Cybersecurity Topics (Crash Course) - EDR, ITDR, Quantum Computing.
📘 Cybersecurity Regulations & Standards - HK, SG, ISA 62443, PCI DSS etc.
‼️Cybersecurity Industry Insights & Quarterly Series - Dec 2023 onwards.
✍️Chronicles of Cybersecurity Consulting Series & few Business lessons.
✍️Must know IT & OT Cybersecurity Series - newsletters, projects, tools, and other resources.
But before we begin, do me a favour and make sure you “Subscribe” to let me know that you care and keep me motivated to publish more. Thanks!
Ready? let’s dive into each of the series.
Alert! some headache / indigestion / is possible if you try to take the following all at once; so take these doze - one series at a time 😀😉.
I hope this helps in your journey. Let me know if it does!
Wishing you all the best.
Warning: Gmail / other email provider may clip this as its long so be sure to click “Read Online” link on the top right hand of the email.
Securing Things Academy: (coming soon)
IT & OT CySEAT (Cyber Security Education And Transformation) course is designed for IT and OT cybersecurity practitioners. Join the wait-list → here.
Checkout a brief overview below:
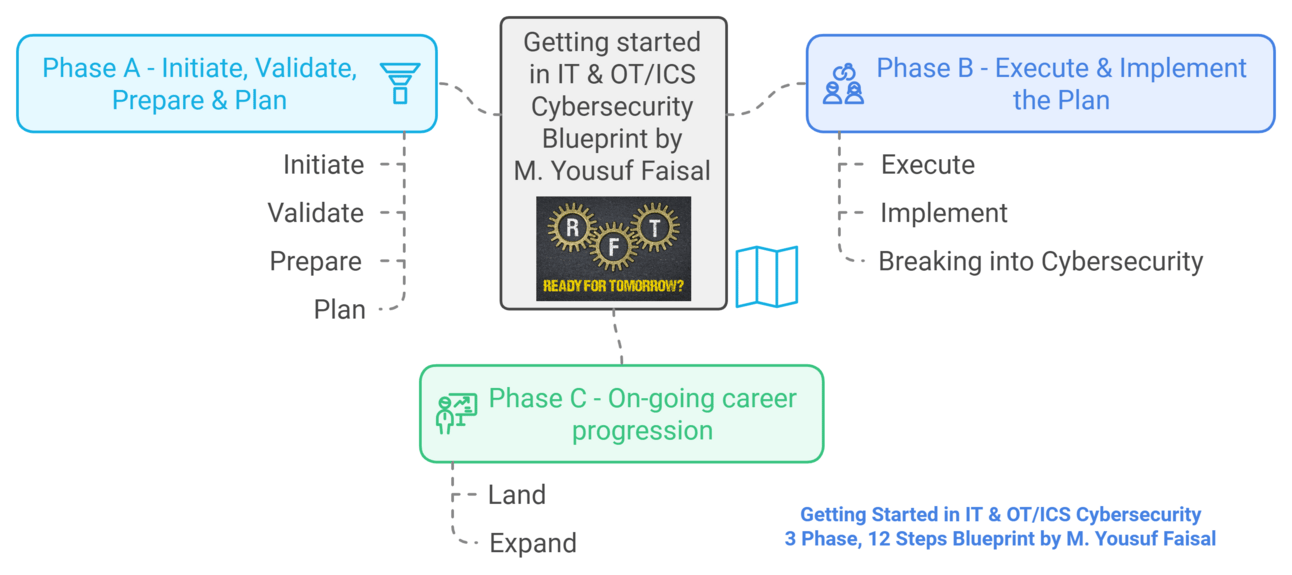
Getting Started in IT & OT Cybersecurity
Since starting the newsletter, I’ve had several folks DM me on how to get started and or what to do next, these repeated questions and I noticed many professionals and upcoming grads are confused / troubled with all the noise out there.
Therefore, I spend a weekend thinking what would I do if I’d be starting and or if I were transitioning in my career? The answer is the following 3 phase and 12 step blueprint.
I wish I had one, when I was getting started in my career.
Is this perfect?
Ans: Likely not. But I am hopeful and confident that it’ll help carve out your own unique blueprint and so that you have to struggle a bit less. All the best!
Getting started in IT & OT Cybersecurity - A 3 phase & 12 steps blueprint.
Phase A - Initiate, Validate, Prepare & Plan
👉Step 1 – Get to know the Industry, stakeholders, critical infrastructure sectors & the ecosystems – research & get excited.
👉Step 2 – Learn IT & OT/ICS basics - acronyms, device types, famous attacks, key differences between IT & OT, and more.
👉Step 3 – Mappings across IT/OT processes, layers of Automation stack, Purdue Model & domain specific knowledge areas.
👉Step 4 – Know the career tracks / options (tasks / skills) & craft a career + progression plan.
Coming soon…
Phase B - Execute & Implement the Plan - Breaking into Cybersecurity
👉 Step 5 – Trainings (possibly get certified) (Theory + Practical / hands-on / CTF) (both free & paid).
👉Step 6 – Learn few local / regional / international best practices guidance, standards & regulations.
👉 Step 7 – Find experts / mentor(s), connect & build professional network (find potential projects).
👉 Step 8 – Build resume, online profiles, get connected / network, interview & break into cybersecurity.
Phase C - On-going career progression - Land and expand
👉Step 9 – Gain experience & stay up-to-date with industry events / changes via online/in-person forums, communities & more.
👉Step 10 – Advance training/certs to expand hard (e.g. technical) & soft skills (e.g. leadership, presentation/communications etc.).
👉Step 11 – Several resources to subscribe to —> Read | Watch | Listen | & Practice.
👉Step 12 – Continuously Learn | Unlearn | Learn per industry trends, personal branding & more.
🙂Hope this is maybe of some value and or transformative for you.
Note:
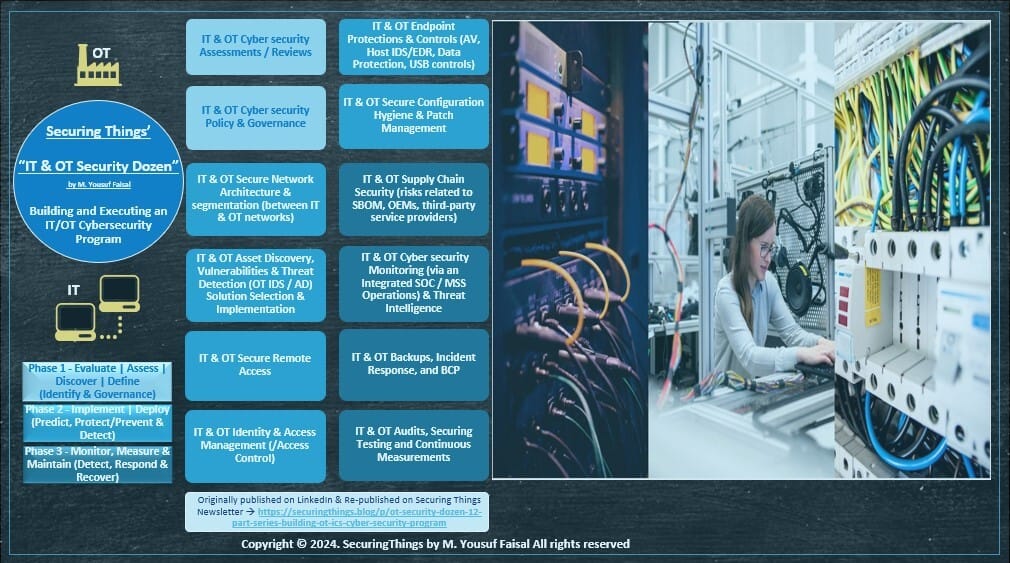
The OT Security Dozen Series
The series is inspired by the framework (/an approach) I’ve build and used in last few years to help few and after speaking to many industrial organisations, building an OT Cybersecurity program from Strategy to Execution.
The OT Security Dozen - a 12 Part series on Building an OT/ICS Cybersecurity Program:
Phase 1 - Evaluate | Assess | Discover | Define (Identify)
Part 1 - OT / ICS Cyber security Assessments / Reviews.
Part 2 - OT / ICS Cyber security Policy & Governance.
Phase 2 - Implement | Deploy (Predict, Protect & Detect)
Part 3 - OT / ICS Network security Architecture & Segmentation (between IT & OT networks).
Part 4 - OT / ICS Asset Discovery, Vulnerabilities & Threat Detection (or OT IDS / AD) Solution Selection & Implementation.
Part 5 - OT / ICS Secure Remote Access.
Part 6 - OT / ICS Access Control (IDAM).
Part 7 - OT / ICS Endpoint Protections & Controls (AV, Host IDS/EDR, Data Protection, USB controls).
Part 8 - OT / ICS Configuration Hygiene & Patch Management.
Phase 3 - Monitor, Maintain & Measure (Detect & Respond)
Part 9 - OT / ICS Supply Chain Security (risks related to SBOM, OEMs, third-party service providers).
Part 10 - OT / ICS Cyber security Monitoring (via an Integrated SOC / MSS Operations) & Threat Intelligence.
Part 11 - OT / ICS Backups, Incident Response & BCP.
Part 12 - OT / ICS Audit, Security Testing & Continuous Measurement.
🙂Hope this is maybe of some value and or transformative for you.
Note: If this is of some value or interest to you and your career, do register your interest in
ISA/IEC 62443 Standards Overview Series
This series is all about an overview of key elements of ISA/IEC 62443 cybersecurity standards and will also include my journey on the certification track.
ISA/IEC 62443 Standards Overview Series - Part 1 - Standards Overview Series, covering key topics on what you need to know.
ISA/IEC 62443 Standards - Part 2 - Standards Overview Series, covering key topics on what you need to know.
ISA/IEC 62443 Standards - Part 3 - Standards Overview Series, covering key topics on what you need to know.
ISA/IEC 62443 Standards - Part 4 - 62443-2-1:2024 Standard updates and more.- Standards Overview Series, covering key topics on what you need to know.
ISA/IEC 62443 Standards - Part 5 - Security Program Elements (SPEs) for 62443-2-1:2024, Upcoming Asset Owner ACS Security Assurance (ACSSA) Certification Scheme to ISA/IEC 62443-2-1, 2-4, 3-2, 3-3 by ISCI, CISO's role, other interesting reads.
ISA/IEC 62443 Standards - Part 6 - 62443-2-2:2025 IACS Security Protection Scheme, ISASecure Certification Standards, upcoming sessions & newsletters✍️ [Securing Things by M. Yousuf Faisal]
More to come…
ISA/IEC 62443 Standards - Part 7 and more.
🙂Hope this is maybe of some value and or transformative for you.
What would you like me to add in near future?
IT/OT Cybersecurity Program Transformation Series
In the below series I am sharing my experience from the field specific to the subject of building and executing Cybersecurity program / transformation for businesses with some supporting IT and OT toolkits.
IT & OT Cybersecurity Strategy - Building an IT & OT/ICS Cybersecurity Strategy.
Presenting IT & OT Cyber-security Strategy - to Executives / Board of Directors.
IT & OT Cybersecurity Strategy, Program, Execution & Management - basics around strategy, program execution and management.
IT & OT/ICS Cybersecurity & Resilience Transformation Program CISO / CIO / CTO's Guide to Cybersecurity & Resilience Transformation Program.
Secure by 3Ds (Demand | Design | Default) ✅ The trifecta reshaping IT & OT cybersecurity industry! Discover what these mean, why they matter, and how they protect critical infrastructure. 🚀
Complexity Ain't an Excuse for OT/ICS Insecurity - Here's How to Lock It Down! Complexity as an Excuse - is NOT a Free Pass, Key Concepts, Surveys vs. Real-World Incident vs. Case Study, Start OT/ICS Cybersecurity Journey, Elevate your OT/ICS Cybersecurity Posture.
Boost Your Defense Game! IT & OT/ICS Cybersecurity Training - Bridging IT & OT gap via Training, Key Stages of Manufacturing Lifecycle and Cybersecurity risks, Breaches - Case Studies / Lessons & STA.
IT & OT/ICS Cybersecurity Policy(/ies) Deciding on the Policy Route for your enterprise cybersecurity needs - both for IT and OT/ICS environments.
CISOs Guide to AI - list of 12 high-level steps CISO’s can take, to start addressing AI risks and 50 Curated References as additional Guidance.
OT/ICS Cybersecurity Requirements Specification for SMB Manufacturers.
OT Security Visibility Solutions & Metrics ✅ Lessons learned consulting on top OT Security Solutions, KPIs/ODMs, & more.
Internal Audit and IT & OT Cybersecurity Program Challenges for Internal Audit Teams and Suggested Approach for Internal Auditors -
IT Cybersecurity Toolkit for Small/Medium Businesses Starting with IT Cybersecurity for your Small or Medium Enterprise Business.
IT & OT Network Security - Example Do's & Don'ts ✅ Deadly Sins (Common Mistakes) & Quick Wins (recommended fixes) for Industrial / Manufacturing environments. Plus CISO's query and my response on Managed vs. Unmanaged switches for production environment
IT & OT Cybersecurity Requirements Specifications — Do’s & Don’ts ✅ Deadly Sins (Common Mistakes) & Quick Wins (recommended fixes) for Cybersecurity requirements specification for Industrial environments 🚨- You Can’t Afford to Ignore! Plus🚨Announcement on OT Cybersecurity Procurement Process & Practices Series - an ultimate guide for IT-OT Tech, Cybersecurity & Procurement Professionals.
More to come…
xxxxxxx
🙂Hope this is maybe of some value and or transformative for you.
What would you like me to add in near future?
Securing Things (Sponsor)
OT CBPRS (Cybersecurity Best Practices Requirements Specification) Toolkit!
The Solution (For Asset Owners Only) - Toolkit to get a head start for your OT/ICS Cybersecurity journey for SMB/SME industrial environment. Bonus - comes with limited complimentary seats for IT & OT CySEAT offering.
Below is a brief walkthrough on the toolkit:
(Note: Next iteration would include the ISA/IEC 62443-2-1 Security Program related requirements).
Cybersecurity & AI across IT-OT Automation Stack
Cybersecurity and AI Across the Industrial Automation Stack - Monthly Digest # 0 ✅ Interested in Industry/Market Insights on layers of automation stack across Cloud, ERP, DMZ, MES, SCADA, HMI, PLC/Edge layers, physical devices & more.
Cybersecurity and AI Across the Industrial Automation Stack - Monthly Digest # 1 ✅ Industry Trends, Market Insights on cybersecurity and AI across the layers of industrial automation stack (Cloud, ERP, DMZ, MES, SCADA, HMI, PLC/Edge), physical devices & more.
Cybersecurity and AI Across IT-OT Automation Stack - Monthly Digest # 2 ✅ Competence Framework for Solutions Architects and Security Architects on industry 4.0, cybersecurity and AI across the automation stack (Cloud, ERP, DMZ, MES, SCADA, HMI, PLC/Edge), physical devices & more.
More to come…
Cybersecurity and AI Across the Industrial Automation Stack - Monthly Digest # 3 ✅.
🙂Hope this is maybe of some value and or transformative for you.
What would you like me to add in near future?
The Digital Factory - Cybersecurity
The Digital Factory (Hub & Spoke) - Part 1 UNS concept, Digital factory, 4.0, data/event driven architecture, industry conferences, and more.
The Digital Factory (Data Flow) - Part 2 Industry 4.0 data/event driven data flows and security considerations and how's CISO's role is evolved in OT security..
More coming soon…
The Digital Factory (Network Architecture) - Part 3 ✅and more.
Other related…
Digital Transformation & Cybersecurity Strategy - Premier - for the digital factory.
Digital Manufacturing at Risk - Start with Cybersecurity and Digital Transformation Maturity Assessment Reviews Now! 📢 Cybersecurity or Digital Transformation Maturity Assessment + Sample Request for information (RFI)!🛡️& Cyber Defense Matrix across Automation Stack.
Role of AI & Cybersecurity in Manufacturing - Use Cases, Predictions, Threats, Mitigations
🙂Hope this is maybe of some value and or transformative for you.
What would you like me to add in near future?
Misc. Cybersecurity Topics - Crash Course Style
Endpoint Detection & Response (EDR) Solutions for IT & OT/ICS.
Quantum Computing Cybersecurity Crash Course - Quantum Computing basics and the Future Cybersecurity Concerns.
What the heck is ITDR? A Crash Course on Identity Threat Detection & Response (ITDR) and its role in Identity Security Ecosystem.
More to come…
🙂Hope this is maybe of some value and or transformative for you.
What would you like me to add in near future?
Cybersecurity Regulations & Standards
Cybersecurity & Data Privacy for Hong Kong - Latest Critical Infrastructure Bill 2024 regulations, Data Privacy Program Core elements, HK Cybersecurity market insights and more.
ISA/IEC 62443 Standards overview Series (Part 1 - to - 5) - links above.
Singapore CII (Critical Information Infrastructure) CCOP v2 Overview - a brief overview of the standard.
PCI DSS v 4.0 - Overview & Changes - a brief overview of Payment Card Industry Data Security Standard v4.0 release.
More to come…
NIS 2, ISO 27001, and more.
🙂Hope this is maybe of some value and or transformative for you.
What would you like me to add in near future?
Cybersecurity Industry Insights & Quarterly Series
Cybersecurity Reflections on 2023 & 2024 + OT/ICS Topic of the day.
Cybersecurity (IT, OT/ICS, AI, Open source) Insights from Q1 2024.
Cybersecurity (IT, OT/ICS, AI, Open source) Insights from Q2 2024.
Cybersecurity (IT, OT/ICS, AI, Open source) Insights from Q3 2024.
Cybersecurity (IT, OT/ICS, AI, Open source) Insights from Q4 2024.
Unlocking 2025: Must-Know Cybersecurity Predictions for IT, OT, and Beyond! Cybersecurity Predictions for 2025: Are You Ready for the rest of the yea.
Biggest Cybersecurity Acquisition Ever! ✅Google Acquisition of Wiz - a $32B Bet to End “Security Theatre” and future of Multi-Cloud Security, also includes analyst views what this means for the cybersec industry.🚀.
Cybersecurity (IT, OT/ICS, and AI) Insights from Q1 2025.
More to come…
🙂Hope this is maybe of some value and or transformative for you.
What would you like me to add in near future?
Chronicles of Cybersecurity Consulting & Business
Chronicles of Cybersecurity Consulting - 1st in series - The Bleeding Password.
Chronicles of Cybersecurity Consulting - 2nd in series - Shortest Consulting Engagement Ever.
Chronicles of Cybersecurity Consulting - 3rd in series - Assessment Slips to Discovery.
Chronicles of Cybersecurity Consulting - 4th in series - Stress in Cybersecurity ✅ Chronicle of a Remote OT assessment for factory from future & the stressed consultant - with some weird humour. How to identify stress and manage it, some stats and other chronicle - Tales from OT trenches and call out to share yours.
More to come…
2 years of Independent Cybersecurity Consulting & Lessons Learned - sharing personal cybersecurity consulting experience.
This is it - Good Bye. Happy New Year! Recap on 2024 and the Future of Securing Things in 2025.
🙂Hope this is maybe of some value and or transformative for you.
What would you like me to add in near future?
Must know IT & OT Cybersecurity Series
Top IT, OT/ICS & AI Cybersecurity Newsletters - You can't go without.
Must know OT Security Projects & Trainings ✅Few Free OT Security tools & trainings for your OT security team and program.🚀.
Top Books for Cybersec Leaders & Pros! (Must Read / Listen) ✅My list of IT-OT & Cybersecurity, Leadership, Productivity, Personal Development, and Money/Business books - must read for Cyber Leaders and Practitioners. Few updates on OT Security conference, & more.
Seems these were the most viral posts with most views from social.
My Recent Most Viewed Social Posts
In case you’ve missed - here are some of my recent most viewed social posts.
📢 Must know OT Security Projects & Trainings ✅Few Free OT Security tools & trainings for your OT security team and program.🚀 [SecuringThings by M. Yousuf Faisal] 🗞️ —>5800 views in 3 days.
Cybersecurity and AI Across the Industrial Automation Stack - Monthly Digest # 1 - ✅ Industry Trends, Market Insights on cybersecurity and AI across the layers of industrial automation stack (Cloud, ERP, DMZ, MES, SCADA, HMI, PLC/Edge), physical devices & more.🚀 [Securing Things by M. Yousuf Faisal].
ISA/IEC 62443 Standards - Part 5 - Security Program Elements (SPEs) for 62443-2-1:2024, Upcoming Asset Owner ACS Security Assurance (ACSSA) Certification Scheme to ISA/IEC 62443-2-1, 2-4, 3-2, 3-3 by ISCI, CISO's role, other interesting reads.
The Digital Factory (Data Flow) - Part 2 Industry 4.0 data/event driven data flows and security considerations and how's CISO's role is evolved in OT security.
Cybersecurity & Data Privacy for Hong Kong - HK Cybersecurity Market, upcoming Critical Infrastructure Bill 2024 regulations, Data Privacy Program Core elements, HK markets and more.
Biggest Cybersecurity Acquisition Ever - ✅Google Acquisition of Wiz - a $32B Bet to End “Security Theatre” and future of Multi-Cloud Security, also includes analyst views what this means for the cybersec industry.🚀 [Securing Things by M. Yousuf Faisal]
📢 📰 Secure by 3Ds (Demand | Design | Default) 📢 📰 ✅ The trifecta reshaping IT & OT cybersecurity industry!
What the heck is ITDR - A crash course on Identity Threat Detection & Response.
Ways in which I can help?
Whenever you are ready - I can help you with:
A - IT & OT Cybersecurity Advisory / Consulting services - for securing your business and or its digital transformation journey.
B - Security Awareness Training & Phishing Awareness Portal - Train your staff and build a Security awareness program through our subscription based service.
C - Securing Things Academy (STA) - Security trainings for IT & OT practitioners.
Visit the newsletter website for Links to above services and or reach out at info[at]securingthings[dot]com or DM me via LinkedIn.
D - Securing Things Newsletter - Sponsor this newsletter to showcase your brand globally, or subscribe to simply Get Smarter at Securing Things.
Reach out at newsletter[at]securingthings[dot]com or DM me via LinkedIn.
✉️ Wrapping Up
Have questions, comments, or feedback? Just reply directly, I’d love to hear from you.
Also, if you find this or previous newsletter edition(s) useful and know other people who would too, I'd really appreciate if you'd forward it to them. Thanks a ton.
Thanks for reading - until the next edition!
It’s a Great Day to Start Securing Things for a Smart & Safer Society.
Take care and Best Regards,
Rate the newsletter content
If you are reading this online don’t forget to register; validate your email, and request a login link to submit the poll.
Your feedback and input is invaluable to me as we work together to strengthen our cybersecurity defenses and create a safer and smarter digital society. Thank you for your trust and continued support.