Disclaimer: All views presented here, in this newsletter, are my own.
Author or the newsletter are not liable for any actions taken by any individual or any organization / business / entity. The information provided is for education and awareness and is not specific to any business or situation.

Table of Contents
Continuing from one of the previous newsletter posts titled - Digital Transformation & Cybersecurity Premier (an introduction) and IT & OT/ICS Cybersecurity Strategy that talks about drafting an integrated IT and OT/ICS Cybersecurity strategy or independent ones. In case you've missed them - highly recommend reading them first before reading this edition of newsletter.
So let's get started.
Now that we've laid out high level steps of #digitaltransformation and #cybersecurity #strategy journey and then have finished drafting/developing the cybersecurity strategy (phase 1 in strategy life-cycle), the next step is preparing and presenting the cybersecurity strategy to business executives and or to the board of directors to get their buy-in and approval for funding, executive commitment and resources required to executive the strategy (which is phase 2 in the strategy cycle).
This is probably one of the most daunting and difficult task for many, specially for people with technical skills and no management background or business skills, and many struggle to get the message across and don't get the right level of support or funding from business leaders/executives. One would need to remove their technical hats and put on their business hats, to simplify the messaging around cyber risks equation, focus on risks and consequences that their organization is potentially exposed to.
On daily basis, the business executives and board of directors are ensuring that they are taking the right decisions to move the business forward by managing varying types of risks (financial, reputation, legal, environmental, ESG, operational, etc.) that their business operations need addressing, so that their investments decisions are prioritized.
Before the Presentation
Research the executive audience you'll be presenting to (what they like to discuss/interests, persona types etc.). If you personally know them you may have an advantage (but in some cases, it’s likely that you don't interact them on daily basis), if you don’t; do ask people around that have given presentations and take into account their feedback on what works and what may not work.
Presentation (Content Preparation-to-Delivery)
The Story line
Make it sound like you are taking them on a short, precise, quick journey where you are projecting the current state of affairs, what's your recommended target state looks like and what would it take the business to achieve the target state - i.e. a managed risk state.
Presentation Content
Below highlights an example Agenda:
Agenda/Presentation Title - choose a catchy agenda title that could draw attention (that something important is coming) - and may resonate with business vision and or business priority goals. E.g.:
Global Cyber-security Strategy (2023-2026) or
IT & OT/ICS Cyber-security Strategy & Program Road-map - A structured risk reduction approach.
Note: choose your own environment and best scenario specific titles.
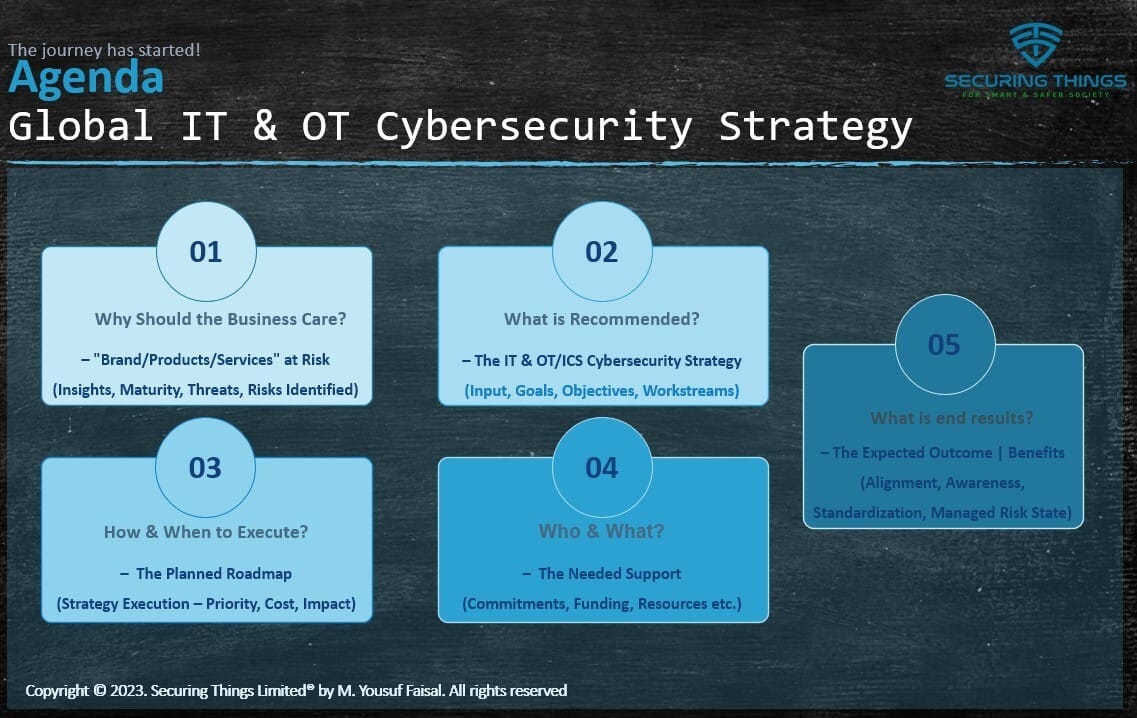
Example STL IT & OT Cybersecurity Strategy Presentation Agenda
note:
Brand Name/Products/Services could be replaced by your specific business elements e.g. X Food & X Beverages brand or product names / services - anything that's business specific.
depending upon the executive leadership style, some would prefer the asks i.e. item 4 in above picture to be put in front earlier in the presentation, before you talk about 2 and 3. Therefore, adjust accordingly).
Ensure you understand the current business climate and situation and if its the right time to ask in the first place. Budget submission period is perfect but you need to spread the awareness among peers and other parts of business well in advance to get a buy-in in time for the budget.
Be as specific and precise as possible on the asks from the executives (e.g., resource requirements, staff involvement, approvals and funding etc.).
Taking Inspiration from different experts from the field
Its great to learn from experts that share some wonderful techniques on how they are moving ahead with their plans, what hurdles they face and how they've overcome them including ideas on what to present and what not to cover.
Below are a list of few of many such great video presentations for reference:
Cybersecurity Leadership - YouTube (112 videos by #sansinstitute #cybersecurityleadership series - play list) (many presenters to thank for).
Presentation Delivery:
You'll likely only have 30 mins to an hour (if you are lucky) to get your message across and get your messaging stick with executives. So prepare, do some dry runs with colleagues/team, modify adjust.
Be ready to request for another time and or shorten your presentation as it’s far too often that something urgent will come at last minute. So let’s say you should have 15 mins of speech in mind in case the original time slots shortens up.
Tips: Checkout the above example videos to get insightful tips and approaches.
Takeaways:
Executives and board care about (or tasked to do so) the following few things:
risks (regulatory, security, brand/reputation, financial, innovation or lack thereof),
revenue / mission and
costs (do more with less)
customers and shareholders.
- a secure, standardized and resilient business operations helps drive all these things towards positive direction and the presentation should touch upon the above points to emphasis benefits across these points.
Good luck for your next IT & OT (or one of them) Cybersecurity Strategy & Road-map presentation internally or to your clients/customers.
In case its time for presenting your 1st IT & OT Cybersecurity Strategy or time for an update/re-write - feel free to reach out to me via DM or get in touch at info[@]securingthings[dot]com for any business needs, project support, discussions and or simply information sharing.
Securing Things Academy:
IT & OT CySEAT (Cyber Security Education And Transformation) course is designed for IT and OT cybersecurity practitioners. Join the wait-list → here.
Checkout a brief overview below:
Ways in which I can help?
Whenever you are ready - I can help you with:
A - IT & OT Cybersecurity Advisory / Consulting services - for securing your business and or its digital transformation journey.
B - Security Awareness Training & Phishing Awareness Portal - Train your staff and build a Security awareness progthroour subscription based service.
C - Securing Things Academy (STA) - Security trainings for IT & OT practitioners.
Visit the newsletter website for Links to above services and or reach out at info[at]securingthings[dot]com or DM me via LinkedIn.
D - Securing Things Newsletter - Sponsor this newsletter to showcase your brand globally, or subscribe to simply Get Smarter at Securing Things.
Reach out at newsletter[at]securingthings[dot]com or DM me via LinkedIn.
How are we doing?
I invite you as part of #SecuringThings community to share your feedback.
Rate the newsletter content
Your feedback and input is invaluable to me as we work together to strengthen our cybersecurity defenses and create a safer and smarter digital society.
Let us know how we can improve this and or what you’d like to see in future?
Thank you for your trust and continued support.
Do register, validate your email, and request login link to submit poll to be able to enter a chance to win a future course giveaway.
Thanks for reading - until the next edition!
It’s a Great Day to Start Securing Things for a Smart & Safer Society.
Take care and Best Regards,
M. Yousuf Faisal. (Advice | Consult Cyber & business leaders in their journey on Securing Things (IT, OT/ICS, IIOT, digital transformation, Industry 4.0, & AI) & share everything I learn on this Newsletter | and upcoming Academy).
The Newsletter Platform Built for Growth
When starting a newsletter, there are plenty of choices. But there’s only one publishing tool built to help you grow your publications as quickly and sustainably as possible.
beehiiv was founded by some of the earliest employees of the Morning Brew, and they know what it takes to grow a newsletter from zero to millions.
The all-in-one publishing suite comes with built-in growth tools, customization, and best-in-class analytics that actually move the needle - all in an easy-to-use interface.
Not to mention—responsive audience polls, a custom referral program, SEO-optimized webpages, and so much more.
If you’ve considered starting a newsletter, there’s no better place to get started and no better time than now.


