Disclaimer: All views presented here, in this newsletter, are my own.
Author or the newsletter are not liable for any actions taken by any individual or any organization / business / entity. The information provided is for education and awareness purposes only and is not specific to any business and or situation.
Hey there,
Hope you are doing well as we start Q2 2025.
Here are few interesting projects / initiatives that maybe useful for your OT Security team and OT Security Program.
Featuring in no particular order:
✍️ Free assessment tools for facility reviews - CSET and FCF.
📘 A tool for visualizing cybersecurity decisions - CDD by Sarah fluchs.
‼️ Tool to identify OT/IOT assets easily - ICS Rank by Sulaiman Alhasawi.
↪️ Open source project for OT labs - GRFICS by David Formby.
↪️ Lab to test your OT security monitoring - LabShack by Zakhar Bernhardt.
📲 Monitoring of ICS Vulnerabilities → ICS Advisory Project by Dan Ricci.
🧑🎓 Free OT Security Training → by CISA and Mike Holcomb YouTube series.
✍️ Securing Things - your favourite newsletter 😉
Fee other resources.
But before we begin, do me a favour and make sure you “Subscribe” to let me know that you care and keep me motivated to publish more. Thanks!
Ready? let’s dig in.
Yours truly.
— Yousuf.
Securing Things Academy:
IT & OT CySEAT (Cyber Security Education And Transformation) course is designed for IT and OT cybersecurity practitioners. Join the wait-list → here.
Checkout a brief overview below:
Alert! some indigestion is possible to take into so many of these, all at once; so take the following doze - one at a time - 😀.
I hope this helps in your journey. Let me know if it does!
Must know Projects / Initiatives / Tools / Trainings:
There are plenty, but I’d like to cover some handful of interesting ones that you can leverage as part of your OT security team training and assist in OT Security program.
Facility Cybersecurity Framework (FCF) - FCF assessments helps facility owners and operators manage their cyber security risks in their Operations Technology (OT) & Information Technology (IT) networks. FCF strictly follows the National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF).
CSET Tool - CSET v12.2.1.0 - Cyber Security Evaluation Tool (CSET) provides a repeatable approach for evaluating an organization’s security posture. A desktop software tool that guides asset owners and operators through a step-by-step process to evaluate industrial control system (ICS) and information technology (IT) network security practices. Users can evaluate their own cybersecurity stance using many recognized government and industry standards and recommendations.
ICS Rank - by Sulaiman Alhasawi, Discover, Assess, Secure: ICSRank - Your ICS/OT OSINT Solution. ICSRank is designed to aid in the discovery and security assessment of ICS/OT/IIOT devices across the internet. Leveraging the power of leading search engines such as Shodan, Censys, and Google providing insights on attack surface management of industrial systems.

ICS Rank Tool - web page
Cyber Decision Diagram - developed, hosted by Admeritia and lead by Sarah Fluchs. A tool for visualizing cybersecurity decisions. For anyone who needs to understand tech it provides clarity for Complex Cybersecurity Decisions. Effortlessly understand technical systems, focus on real-world impacts, and make cybersecurity decisions confidently—regardless the complexity of your technology.
“The Cyber Decision Diagrams tool took just a few months to build. But the idea behind it took eight years, countless cybersecurity engineering projects across industries, a three-year research project and a PhD,” Fluchs explained.
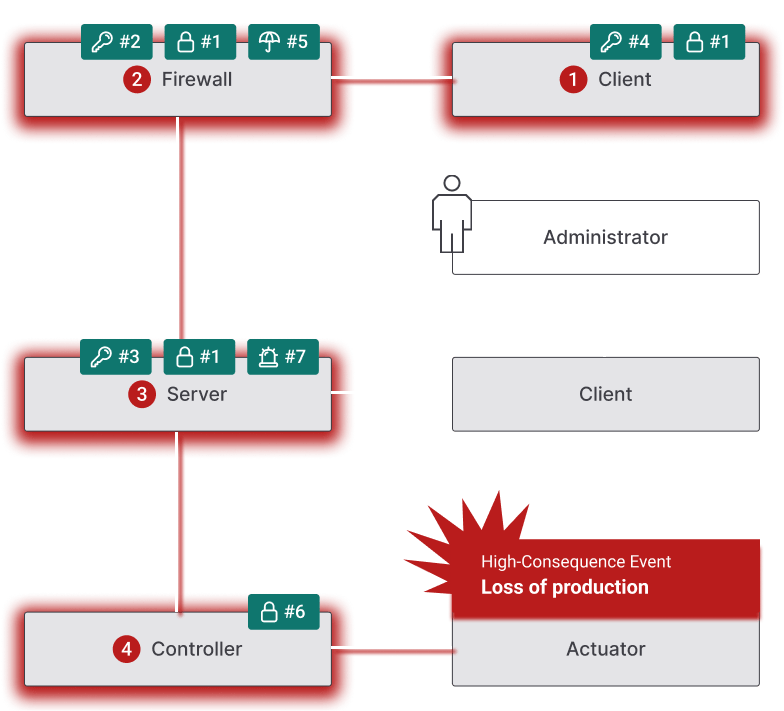
Cyber Decision Diagram
ICS Advisory Project - by Dan Ricci, is an open-source project to provide DHS CISA ICS Advisories data visualized as a Dashboard and in Comma Separated Value (CSV) format to support vulnerability analysis for the OT/ICS community.

ICS Advisory Project Dashboard example
GRFICS - Graphical Realism Framework for Industrial Control Simulations - by David Formby from Fortiphyd is an open source framework for realistic industrial control simulations that uses Unity 3D game engine for simulating industrial control systems.

GRFICS lab screenshot
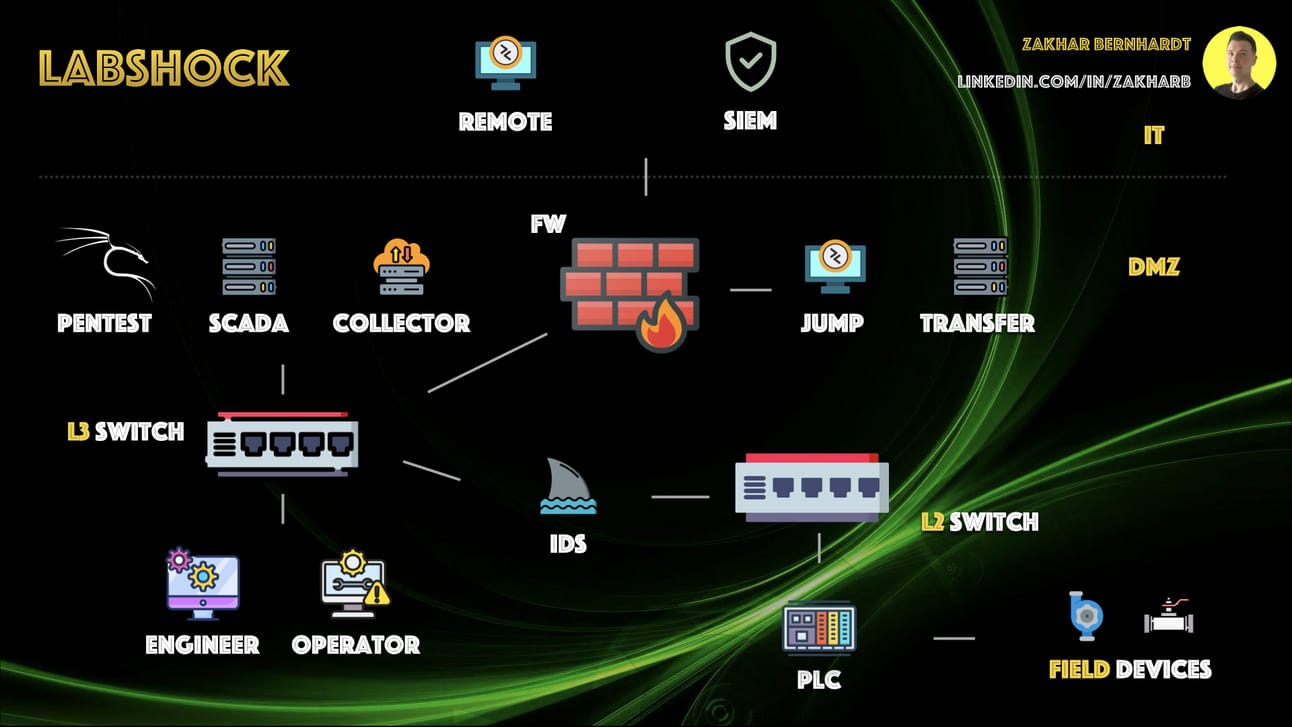
Labshock - by Zakhar Bernhardt. Build and test your ICS Security Lab without expensive hardware / Cost & Complexity.
Free ICS Training by Mike Holcomb → YouTube.
ICS Training Available Through CISA → Free Training Page.
Securing Things newsletter - hopefully your favourite 😉- where I share things about getting smarter at cybersecurity, CISOs guidance on IT, OT/ICS and AI Cybersecurity Program related experience, standards, industry insights.
What would you add? Add even if its some humour 🙂
Few Other resources
GitHub - a large collection of OT/ICS resource list.
A Collection of Resources for Getting Started in ICS/SCADA Cybersecurity - by Rob Lee.
GitHub - awesome-industrial-control-system-security - A curated list of resources related to Industrial Control System (ICS) security.
SANS ICS Resource page.
ISA Resource page.
My Recent Most Viewed Social Posts
In case you’ve missed - here are some of my recent most viewed social posts.
Cybersecurity and AI Across the Industrial Automation Stack - Monthly Digest # 1 - ✅ Industry Trends, Market Insights on cybersecurity and AI across the layers of industrial automation stack (Cloud, ERP, DMZ, MES, SCADA, HMI, PLC/Edge), physical devices & more.🚀 [Securing Things by M. Yousuf Faisal].
ISA/IEC 62443 Standards - Part 5 - Security Program Elements (SPEs) for 62443-2-1:2024, Upcoming Asset Owner ACS Security Assurance (ACSSA) Certification Scheme to ISA/IEC 62443-2-1, 2-4, 3-2, 3-3 by ISCI, CISO's role, other interesting reads.
The Digital Factory (Data Flow) - Part 2 Industry 4.0 data/event driven data flows and security considerations and how's CISO's role is evolved in OT security.
Cybersecurity & Data Privacy for Hong Kong - HK Cybersecurity Market, upcoming Critical Infrastructure Bill 2024 regulations, Data Privacy Program Core elements, HK markets and more.
Biggest Cybersecurity Acquisition Ever - ✅Google Acquisition of Wiz - a $32B Bet to End “Security Theatre” and future of Multi-Cloud Security, also includes analyst views what this means for the cybersec industry.🚀 [Securing Things by M. Yousuf Faisal]
📢 📰 Secure by 3Ds (Demand | Design | Default) 📢 📰 ✅ The trifecta reshaping IT & OT cybersecurity industry!
What the heck is ITDR - A crash course on Identity Threat Detection & Response.
Securing Things Academy:
IT & OT CySEAT (Cyber Security Education And Transformation) course is designed for IT and OT cybersecurity practitioners. Join the wait-list → here.
Checkout a brief overview below:
Ways in which I can help?
Whenever you are ready - I can help you with:
A - IT & OT Cybersecurity Advisory / Consulting services - for securing your business and or its digital transformation journey.
B - Security Awareness Training & Phishing Awareness Portal - Train your staff and build a Security awareness program subscription based service.
C - Securing Things Academy (STA) - Security trainings for IT & OT practitioners.
Visit the newsletter website for Links to above services and or reach out at info[at]securingthings[dot]com or DM me via LinkedIn.
D - Securing Things Newsletter - Sponsor this newsletter to showcase your brand globally, or subscribe to simply Get Smarter at Securing Things.
Reach out at newsletter[at]securingthings[dot]com or DM me via LinkedIn.
✉️ Wrapping Up - How are we doing?
Have questions, comments, or feedback? Just reply directly, I’d love to hear from you.
Also, if you find this or previous newsletter edition(s) useful and know other people who would too, I'd really appreciate if you'd forward it to them. Thanks a ton.
Thanks for reading - until the next edition!
It’s a Great Day to Start Securing Things for a Smart & Safer Society.
Take care and Best Regards,
M. Yousuf Faisal. (Advice | Consult Cyber & business leaders in their journey on Securing Things (IT, OT/ICS, IIOT, digital transformation, Industry 4.0, & AI) & share everything I learn on this Newsletter | and upcoming Academy).
Rate the newsletter content
If you are reading this online don’t forget to register; validate your email, and request a login link to submit the poll.
Your feedback and input is invaluable to me as we work together to strengthen our cybersecurity defenses and create a safer and smarter digital society. Thank you for your trust and continued support.


