Disclaimer: All views presented here, in this newsletter, are my own.
Author or the newsletter are not liable for any actions taken by any individual or any organization / business / entity. The information provided is for education and awareness purposes only and is not specific to any business and or situation.
Hello Securing Things Community,
This is Part-3 of a multi-part series on ISA/IEC 62443 standards overview - and will be expanding more on the standards, understand what are zones and conduits, foundational requirements, its relationship with systems and other requirements, applicability of security levels, different parts of the standard across the cybersecurity lifecycle phases, reference architecture and more.
introduction & background about the standards series,
key stakeholders, IACS roles & responsibilities,
4 groups of standards requirements,
3 phase IACS Cybersecurity Lifecycle,
ISA Secure Certifications for Suppliers, Products, Asset owners & individuals,
important terms, definitions & relationships,
Standards series introduction (of each standard part),
Standards elements, security levels, & types of standards requirements.
Quick test: Try to recall the 4 groups in the standards series using the tip from Part 1. If you can't, click the Part 1 link for a reminder. Hope this helps!But before we begin, do me a favour and make sure you hit the “Subscribe” button to let me know that you care or liked and keep me motivated to publish more. Thanks!
Securing Things (Sponsor)
OT CBPRS (Cybersecurity Best Practices Requirements Specification) Toolkit!
The Solution (For Asset Owners Only) - Toolkit to get a head start for your OT/ICS Cybersecurity journey for SMB/SME industrial environment. Bonus - comes with limited complimentary seats for IT & OT CySEAT offering.
Below is a brief walkthrough on the toolkit:
(Note: Next iteration would include the ISA/IEC 62443-2-1 Security Program related requirements).
✅Note: Part 2 included a diagram illustrating the relationship of certain key terms and definitions. There are plans for certain terminology to be updated soon. More on this when new terms get published in future.
➡The 62443 series includes numerous related standards and reports. Clause three of each publication is the source for terms, conventions, and abbreviations.
Security Requirements📜
We’ll start where we left off in Part 2 related to different types of requirements.
IEC62443-3-3 outlines seven foundational requirements (FRs), which are detailed into a series of system requirements (SRs) and requirement enhancements (REs). The standard provides a chart to map SRs and REs to SLs 1 to 4.
<continue reading by registering below>.
The 7 FRs are outlined below. It also shows the flow of requirements between asset owners, system integrators and product manufacturers based on target security levels.
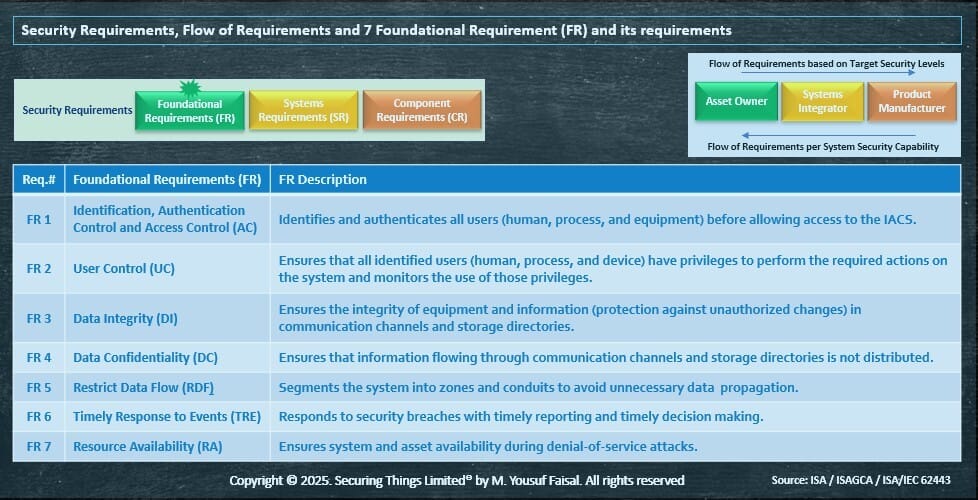
Foundational Requirements
SLs may need adjustment based on security zone differences, threats, operational changes, and technology used, as these factors can alter an ICS's attack surface.
SLs set goals, but these must be flexible and updated to match the evolving threat landscape. Therefore, asset owners should periodically perform risk analysis and also after risk-relevant events to ensure security risks are tracked and SRs remain current, maintaining a defendable posture.
Following image highlights the relationship between the with FRs, SRs and CRs.

Relationship between FR, SR and CR
<Note: I may add an example mapping later>.
Zones, Subzones and Conduits
➡ISA/IEC 62443-3-2 provides guidance on separating an industrial environment into security zones and conduits (defined in Part 2) based on risk assessments. It provides guidance on the selection of and or designing zones, conduits and assigning security levels (SLs).
To achieve the desired SLs, certain countermeasures / controls needs to be implemented to meet a specific SLs.
Asset owners (OT owner / operators) organisations must assess gaps between its existing security controls and the standards definition of assigned levels.
Even with multiple zones, perfect risk isolation in ICS environments is impossible because a weakened zone can impact others by disrupting services or compromise communication paths.
To address this, the standard includes the concept of "conduits" to analyze and protect communication paths / channels between zones.
Each security zone and conduit is assigned a target security level (SL-T).
To achieve a satisfactory security level (SL-A), several factors must be considered.
Though are complex and challenging to implement, the standard outlines these factors.
It's crucial to select and validate countermeasures while considering their implications, such as the impact of function dependency on compromised services in different zones.
Evaluating residual or introduced risks is as important as achieving specific security levels.
When establishing security zones and conduits, these factors must be considered to ensure they meet SL-A.
Communication paths may create residual attack vectors, so they and neighbouring zones must also meet SL-A.

Source: IEC 2033/13 - High-Level Manufacturing Example Showing Zones and Conduits
In segmentation, security zones and subzones are logical constructs separate from the physical network.
Information flows within, into, and out of zones via conduits (communication paths between zones).
These include communications among programming terminals, mobile devices, and vendor connections.
Conduits and channels can be trusted or untrusted, with those not crossing zone boundaries generally trusted.
Untrusted channels occur when parties are at different security levels.
Channels inherit the security properties of their conduits, but secure communications can extend a security zone.
Analysing communications between zones and endpoints is crucial for selecting countermeasures / security controls.
When zones share technologies, they must adopt the higher SL to meet risk-reduction and protection requirements.
This helps identify opportunities for technology segmentation and realignment, minimizing the assignment of higher SLs and reducing costs.
Each OT/ICS solution implementation is unique, but can include following principles:
- Segmentation of ICS, network, and applications offer cost/benefit opportunities.
- Layer 2 network access control can enhance zone boundary controls.
- Zone boundaries create choke points for security monitoring.
- Lower security levels need fewer controls.
- Hierarchical zoning offers defense in depth.
We’ll conclude part 3 here.
Stay tuned to find out more in Part 4 - ISA/IEC 62443 Standards Series Overview in a future newsletter edition, in which we’ll cover, more on the standards, latest revision of 62443-2-1 and what’s new in it, cybersecurity risk assessments using 62443-3-2, applicability of different parts of the standard across the cybersecurity lifecycle phases, and more.
References
ISA main website → https://www.isa.org/
ISA Global Cybersecurity Alliance (ISAGCA) → https://gca.isa.org/resources. e.g.:
Quick Start Guide to ISA/IEC 62443
IoT Security Maturity Model: 62443 Mappings for Asset Owners and Product Suppliers
and more…
Effective ICS Cybersecurity Using the IEC 62443 Standard by SANs.
Few interesting reads / listens
Here are some interesting reads of the week:
Podcast: Enhancing OT Cybersecurity: From Legacy Systems to Cloud Solutions with Paul Shaver - In this episode, Aaron (host) talks to Paul Shaver from Mandiant to navigate the OT cybersecurity landscape.
Read: What the Cyber Resilience Act requires from manufacturers. By Sarah Fluchs provides an interesting brief on upcoming Cyber Resilience Act (CRA) - first regulation worldwide that defines security requirements for products.
Read: Industrial wireless impact on smart manufacturing - In this special report, IEB consulted industry experts on the impact of industrial wireless technology on smart manufacturing. Leaders highlighted trends involving Wi-Fi 6, Wi-Fi 7, and Industrial 5G as effective solutions for manufacturing.
Read: 145,000 systems exposed & many industrial Firms Hit by Attacks - Censys and Kaspersky publish ICS security reports looking into exposure to attacks and actual attacks suffered by industrial organizations.
My Recent Most Viewed Social Posts:
In case you’ve missed - here are some of my recent most viewed social posts.
📰 Unlocking 2025: Must-Know Cybersecurity Predictions for IT, OT, and Beyond! 📰 - outlining few predictions, just another list :-).
The Digital Factory (Hub & Spoke) - UNS concept, Digital factory, 4.0, data/event driven architecture, industry conferences, and more.
OT Security Visibility Solutions & Metrics -✅Lessons learned consulting on top OT Security Solutions, KPIs/ODMs, & more🚀.
Tip to remember ISA/IEC 62443 Standards Group & Overview Part 2.
This is it - Good Bye. Happy New Year! Recap on 2024 and the Future of Securing Things in 2025.
Cybersecurity (IT, OT/ICS, AI, Open source) Insights from Q4 2024.
What the heck is ITDR - A crash course on Identity Threat Detection & Response.
IT & OT/ICS Cybersecurity Policy(/ies) - Deciding on the Policy Route for your industrial environments.
Securing Things Academy:
IT & OT CySEAT (Cyber Security Education And Transformation) course is designed for IT and OT cybersecurity practitioners. Join the wait-list → here.
Checkout a brief overview below:
Ways in which I can help?
Whenever you are ready - I can help you with:
A - IT & OT Cybersecurity Advisory / Consulting services - for securing your business and or its digital transformation journey.
B - Security Awareness Training & Phishing Awareness Portal - Train your staff and build a Security awareness program subscription based service.
C - Securing Things Academy (STA) - Security trainings for IT & OT practitioners.
Visit the newsletter website for Links to above services and or reach out at info[at]securingthings[dot]com or DM me via LinkedIn.
D - Securing Things Newsletter - Sponsor this newsletter to showcase your brand globally, or subscribe to simply Get Smarter at Securing Things.
Reach out at newsletter[at]securingthings[dot]com or DM me via LinkedIn.
✉️ Wrapping Up - How are we doing?
I invite you as part of #SecuringThings community to share your feedback.
Rate the newsletter content
Your feedback and input is invaluable to me as we work together to strengthen our cybersecurity defenses and create a safer and smarter digital society.
Let us know how we can improve this and or what you’d like to see in future?
Thank you for your trust and continued support.
Do register, validate your email, and request login link to submit poll to be able to enter a chance to win a future course giveaway.
Thanks for reading - until the next edition!
It’s a Great Day to Start Securing Things for a Smart & Safer Society.
Take care and Best Regards,
M. Yousuf Faisal. (Advice | Consult Cyber & business leaders in their journey on Securing Things (IT, OT/ICS, IIOT, digital transformation, Industry 4.0, & AI) & share everything I learn on this Newsletter | and upcoming Academy).


